Discover Safe and Secure
Updates with Modino.io
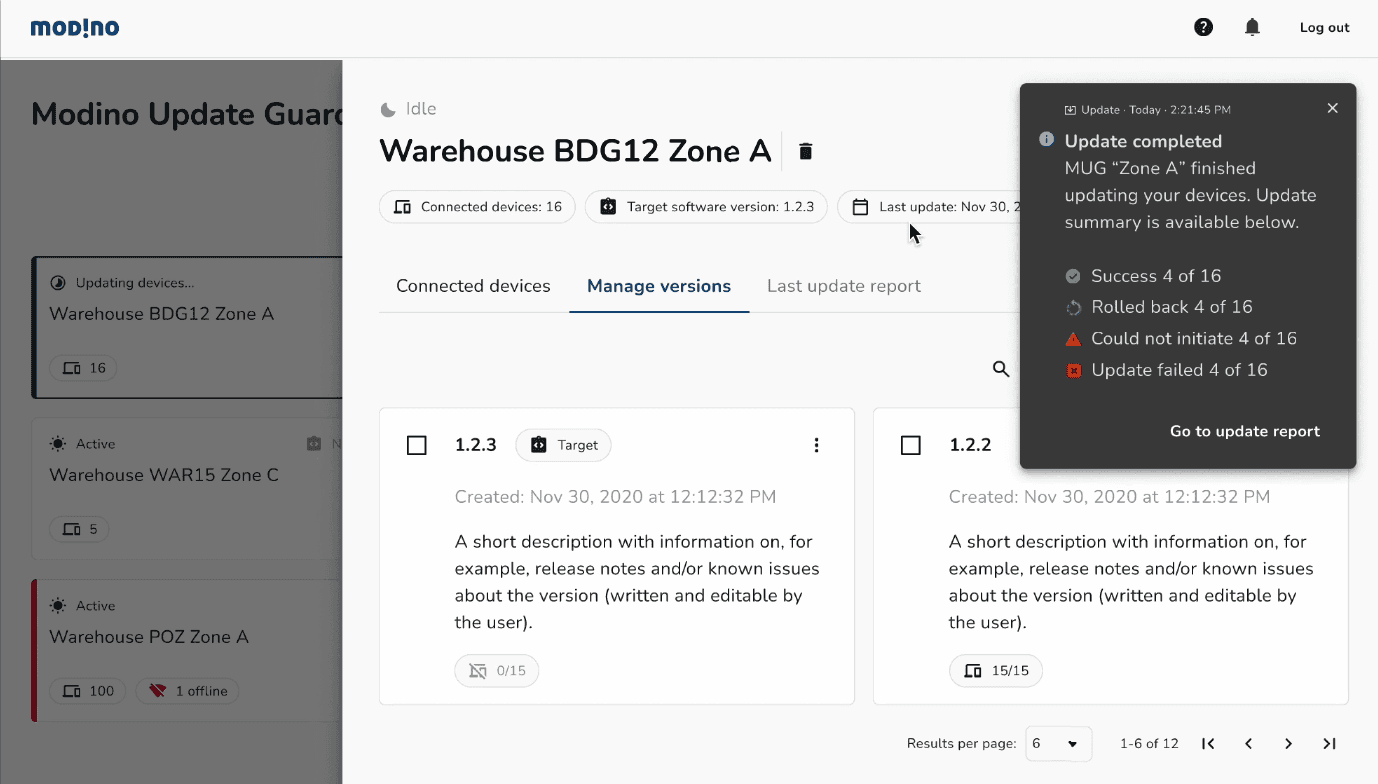
Modino is on-prem & private cloud solution which main goal is to provide software updates for IoT devices in a safe and secure way.
Key aspects

Universal solution
Whether you want to update software on machines, sensors, robots, smart grid or information systems, measuring stations, IP cameras, medical devices, servers, edge cloud infrastructure, or even toys, Modino.io is able to handle it all.

Not hardware bound
Software delivery is hardware-independent. Modino.io containers adapt to the target hardware on IoT devices, enabling updates regardless of the specific hardware architecture and configuration. As long as it runs on a Linux operating system, Modino.io can update it.

Safe software delivery
Atomic updates even in low network throughput environments. Whether you need to update a remote EV charging station or an ATM located in the countryside, Modino.io is able to deliver reliable updates even with limited network throughput.

Ensured software application
With our automatic rollback procedure, your devices will never go offline, even if something goes wrong during the update process.
Security and quality manifesto
Modino.io means safe
Modino.io platform ensures safe software delivery – data to be delivered are created as atomic updates which makes them possible to be send and receive even with low network throughput
Never be offline again - if the update fails, an automatic rollback procedure starts. The device restores to the previous, stable software version, and is still operational.
With a purchased annual license, each client gets regular updates including security, performance patches, and new releases of the Modino.io system.
Security is our second name.
Or, actually, the first
Modino.io is delivered as a set of interconnected OCI containers running in non-privileged mode or when needed with a specifically created security profile. Internally all communication is done via TLS v1.3.
Users are authenticated and authorized like any other system actor with a "zero-trust" policy in mind. User accounts are manageable with a deployed instance of an OpenID Connect service that can be connected with the organization’s user database (e.g. LDAP).
Modino.io Agent installed on endpoint devices does not require administrator privileges to run, and leverages TLS mutual authentication to communicate with Modino.io services.
Container images with software updates are encrypted and signed with user keys that Modino.io does not have access to. No personally identifiable information (PII) is stored.

Awards & Recognitions
Partnerships

We are part of


This project has received funding from the European Union’s Horizon Europe research and innovation programme under the GA 101058613
Advantages
Experience
Our team has more than 15+ years of practical experience in cryptography, encryption and software delivery.
Flexibility
Even if your IoT devices are not natively designed to be updated, Modino.io can do it to keep your business safe.
Monitoring and detection
Modino.io monitors malicious behaviour and provides an active mitigation.
Trust
Your data is yours, Modino.io can't access it since data is encrypted by your keys.